What is NIST CSF?
The National Institute of Standards and Technology (NIST) Cybersecurity Framework (CSF) was published in February 2014, in response to Presidential Executive Order 13636, “Improving Critical Infrastructure Cybersecurity”. This order called for a standardized security framework for critical infrastructure in the United States.
Several governmental entities and a wide range of businesses use the framework to be more proactive about risk management as it provides a high-level taxonomy of cybersecurity outcomes and a methodology to assess and manage them.
The NIST CSF consists of standards, guidelines, and best practices to manage cybersecurity-related risks.
Regardless of the type of organization or its mission, the activities, countermeasures, responsibilities, and objectives of ensuring a robust security posture can be generalized and discussed using the NIST CSF.
The most common applications of the CSF have manifested in three different scenarios:
- Assessment of an organization’s enterprise-wide cybersecurity risk posture
- Assessment of products and services that organizations can control for their conformance to the CSF
- CSF core overlay on existing standards and requirements to assess the risk management practices of technology products and services
What is The Importance of NIST CSF?
Public and private sector entities acknowledge the security value of adopting the NIST CSF and the need for cost-effective solutions to achieve a secure and compliant system and organizational risk posture in a multi-cloud enterprise environment.
NIST CSF is ultimately important for businesses because it provides a comprehensive set of guidelines and best practices for managing and reducing cybersecurity risks. The framework helps organizations to assess their current cybersecurity posture, identify areas where improvements can be made, and establish a risk management program that is tailored to their specific needs.
NIST CSF is an essential tool for businesses that want to protect themselves from cybersecurity risks; here are some key reasons why:
- Risk management: The NIST CSF provides a risk management framework that can help organizations identify, assess, and manage cybersecurity risks more effectively. By following the framework's guidelines, businesses can prioritize their cybersecurity efforts and allocate resources to the areas that need the most attention.
- Compliance: The NIST CSF is widely recognized as a leading cybersecurity standard, and many industries and government agencies require compliance with the framework. Adhering to the NIST CSF can help businesses demonstrate compliance with regulatory requirements and industry standards.
- Business continuity: Cybersecurity incidents can have a significant impact on a business's operations and reputation. The NIST CSF can help businesses develop and implement a plan to prevent, detect, and respond to cybersecurity incidents, ensuring that they can maintain business continuity in the face of a cyber attack.
- Customer trust: Customers expect businesses to take cybersecurity seriously. By following the NIST CSF, businesses can demonstrate to their customers that they have a robust cybersecurity program in place, which can help build trust and enhance the brand's reputation.
The 5 Functions of NIST CSF
The NIST Cybersecurity Framework (CSF) organizes its "core" material into five functions, subdivided into 23 categories. The core functions are:
Identity
Asset management is paramount and usually the first step of cyber security. It is also the most challenging, especially when spread across multiple cloud providers. Maintaining an on-prem and cloud asset inventory has been the most difficult for organizations of all sizes.
Protect
Organizations are required to develop and implement appropriate safeguards to ensure the delivery of critical services.
Detect
The ability to gather, synthesize, and alert on security-relevant events is fundamental to any cybersecurity risk management program.
Respond
Develop and implement appropriate activities following detected security and compliance incidents.
Recover
Enable timely recovery to normal operations to reduce the impact of a cloud-related incident.
The Core references security controls from widely adopted, internationally-recognized standards such as ISO/IEC 27001, NIST 800-53, Control Objectives for Information and Related Technology (COBIT), and ANSI/ISA-62443 Standards-Security for Industrial Automation & Control Systems.
Workstreams For Easy NIST Implementation
The NIST core identifies five key cybersecurity functions to organize recommended security controls into actionable workstreams.
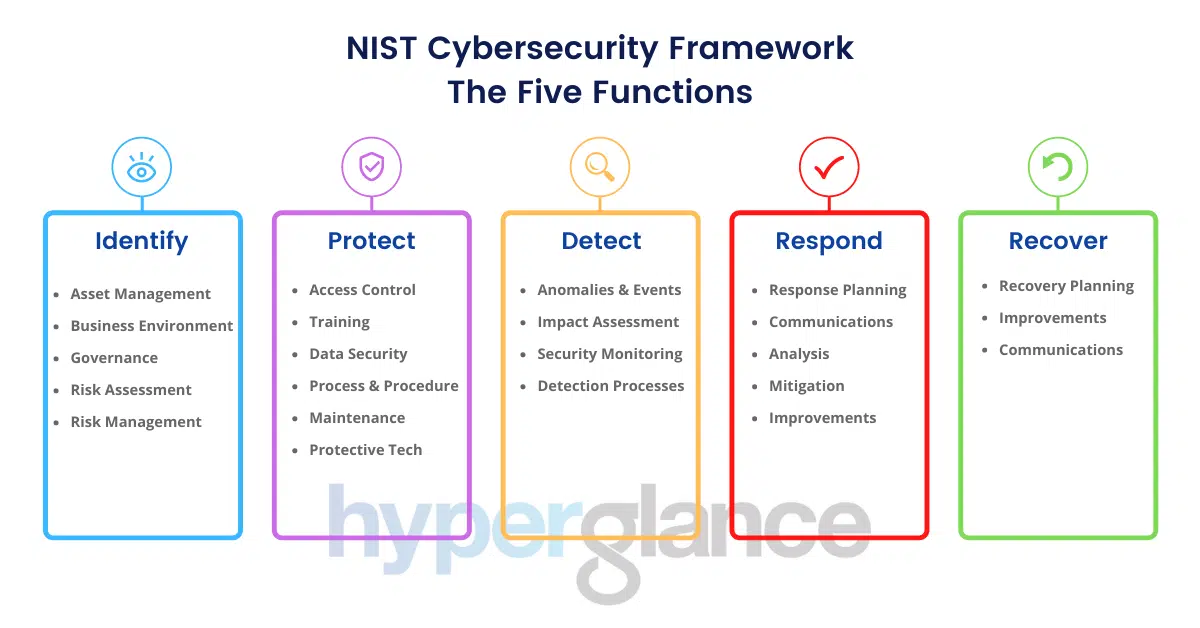
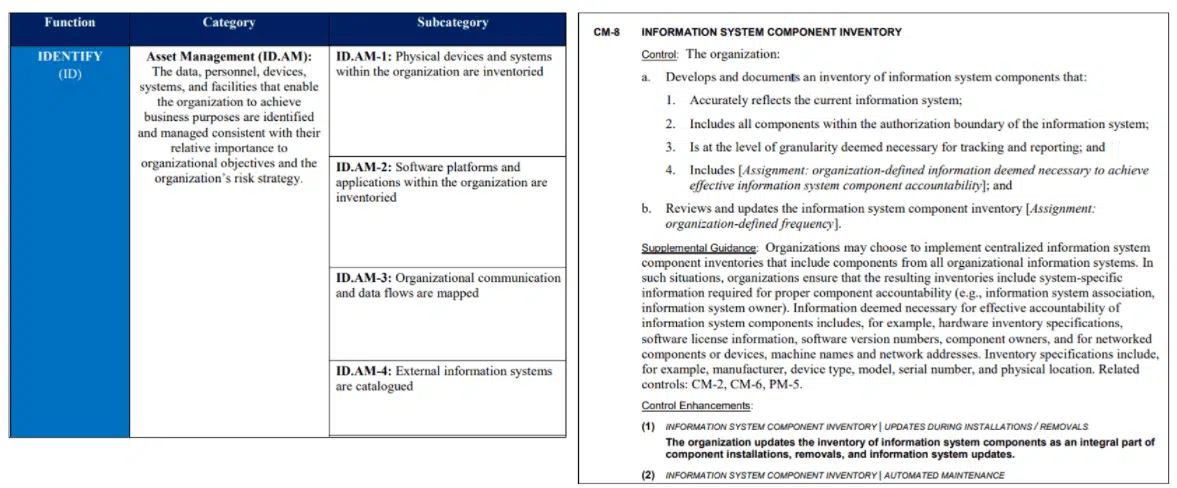
The Framework describes a set of security outcomes to achieve and breaks those into three levels of increasing detail: Functions, Categories, and Subcategories.
Further, each Subcategory contains Informative References. Informative References are materials from other publications that can provide the implementation guidance to achieve those outcomes.
Azure & AWS NIST Compliance
Most cloud providers, including AWS, Azure & Google, have aligned their offerings to the CSF.
However, due to the shared security responsibility model of the cloud, customers have to take steps to align security for their side.
Cloud management shouldn’t involve guesswork, let alone skilled team members spending time on relatively menial tasks and troubleshooting operational problems. Hyperglance ships with solutions designed to help meet security & compliance policies requirements, optimize cost, and more... all in real-time.
How to implement the NIST Cybersecurity Framework using Hyperglance
When the NIST CSF first came to fruition, conducting an assessment was highly manual and time-consuming.
This blog is a first in a series of posts on leveraging Hyperglance to align to the over 100 outcome-based security activities outlined in the NIST CSF.
We will start by mapping the NIST CSF functions to respective Hyperglance features at a high level. We will dive in future publications into the NIST categories and their security controls.
1. Identify
Asset management is paramount and usually the first step of cyber security. It is also the most challenging, especially when spread across multiple cloud providers.
Maintaining an on-prem and cloud asset inventory has been the most difficult for organizations of all sizes.
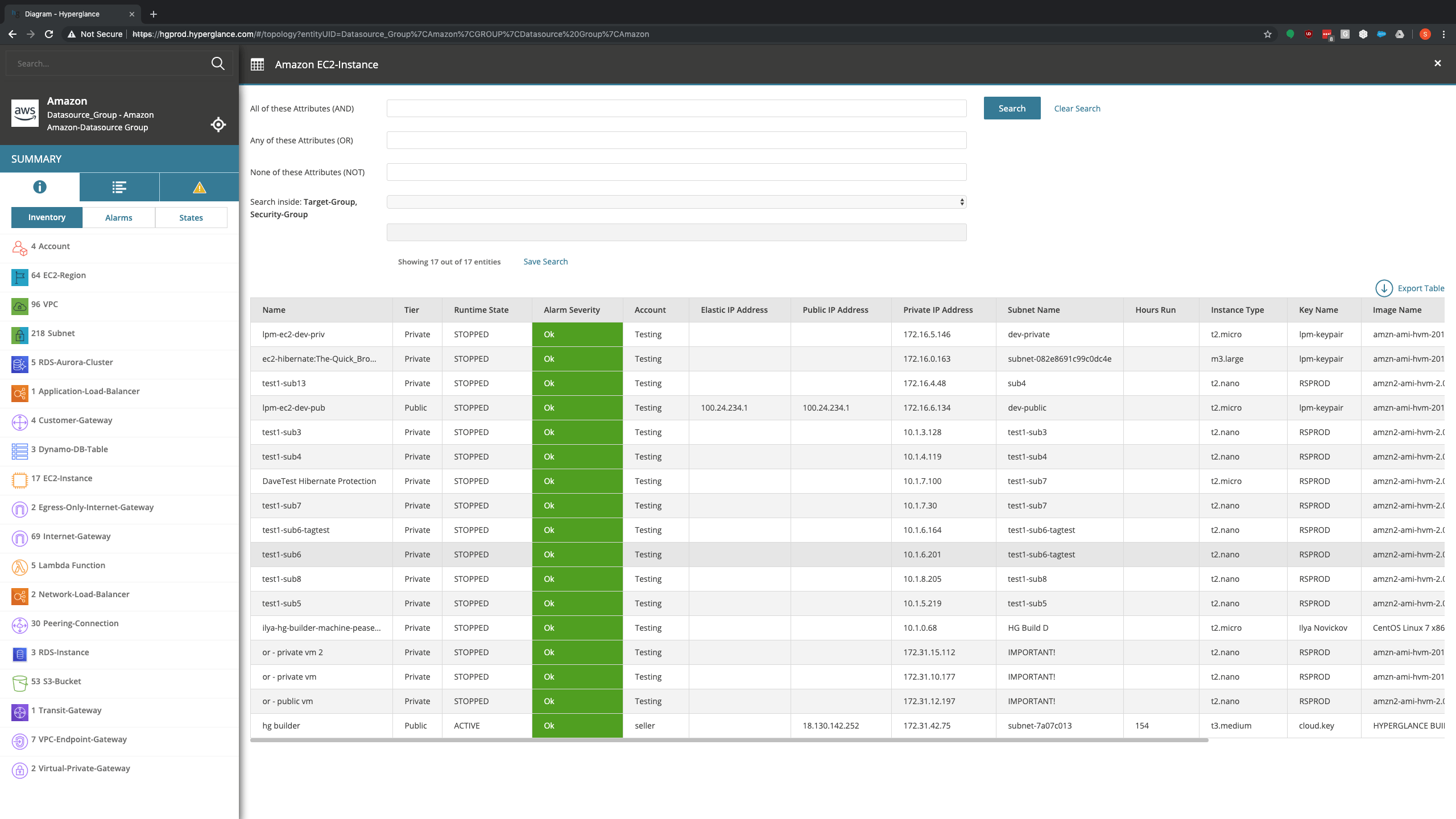
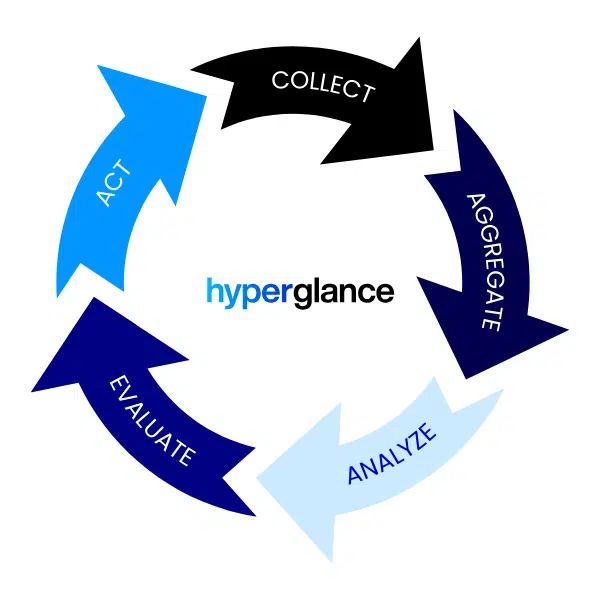
Hyperglance addresses the Identify function by collecting and aggregating all your cloud resources in near real-time.
Based on the cloud Shared Responsibility Model, Cloud providers assume sole responsibility for managing physical assets that comprise their respective cloud infrastructure. Customers are still responsible for maintaining asset inventories for the cloud resources they keep in their environment.
Unlike most offerings available on the market, Hyperglance resides within your cloud boundary, and automatically collects and aggregates cloud resource details across accounts and providers, as well as the dependencies between the respective resources into a single searchable inventory.
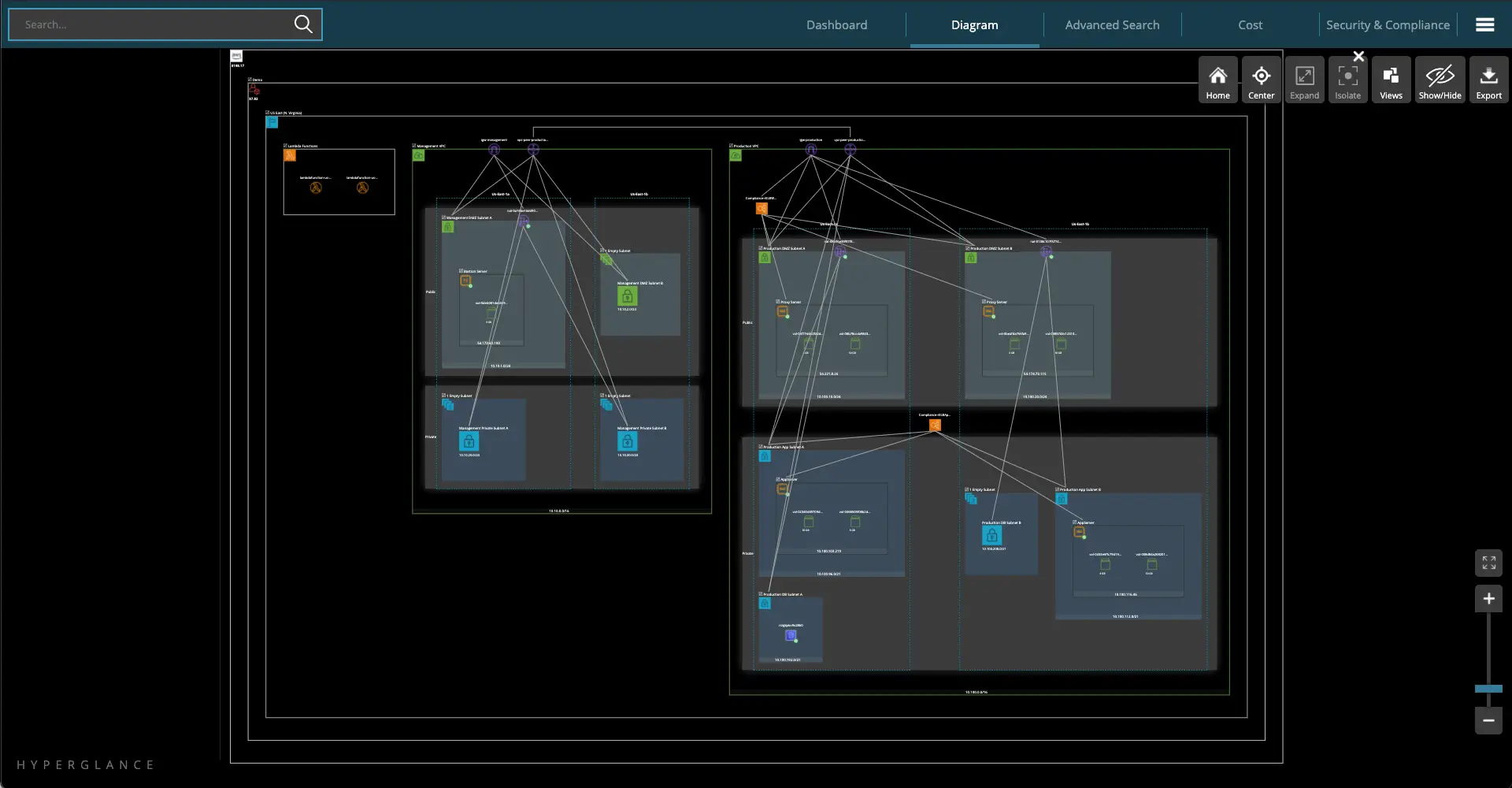
Hyperglance creates a dependency model and also generates an interactive diagram. Great for visualization and exploration of your cloud footprint.
You also have the capability to instantly export your aggregated cloud inventory and topology to CSV, Visio and PNG files.
This is a great and easy way to generate security and compliance-related artefacts such as your Systems Inventory or your System Security Plan.
For even greater visibility into your cloud assets, Hyperglance maps the dependency relationships between your assets into an interactive diagram.
When it's time for an audit, Hyperglance helps you manage stakeholder reviews of your controls, which means you can build audit-ready reports with much less manual effort accompanied by the relevant diagrams.
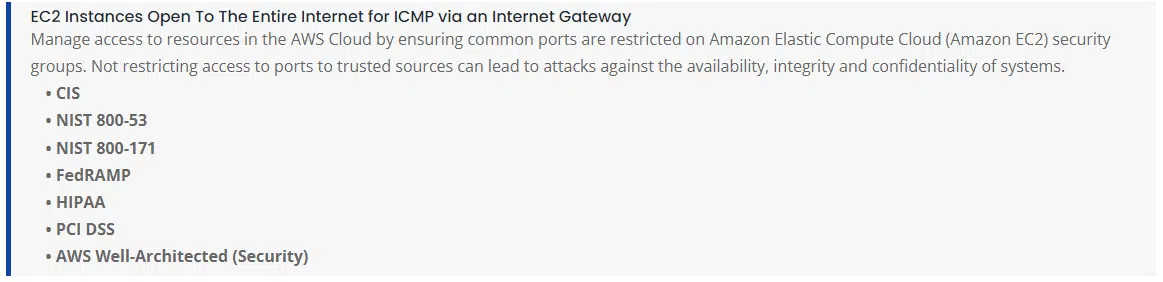
2. Protect
Organizations are required to develop and implement appropriate safeguards to ensure the delivery of critical services.
Hyperglance supports the Protect Function by providing several mechanisms to limit or contain the impact of a potential cybersecurity event by providing visibility into your cloud Identity Management and cloud resources Access Control.
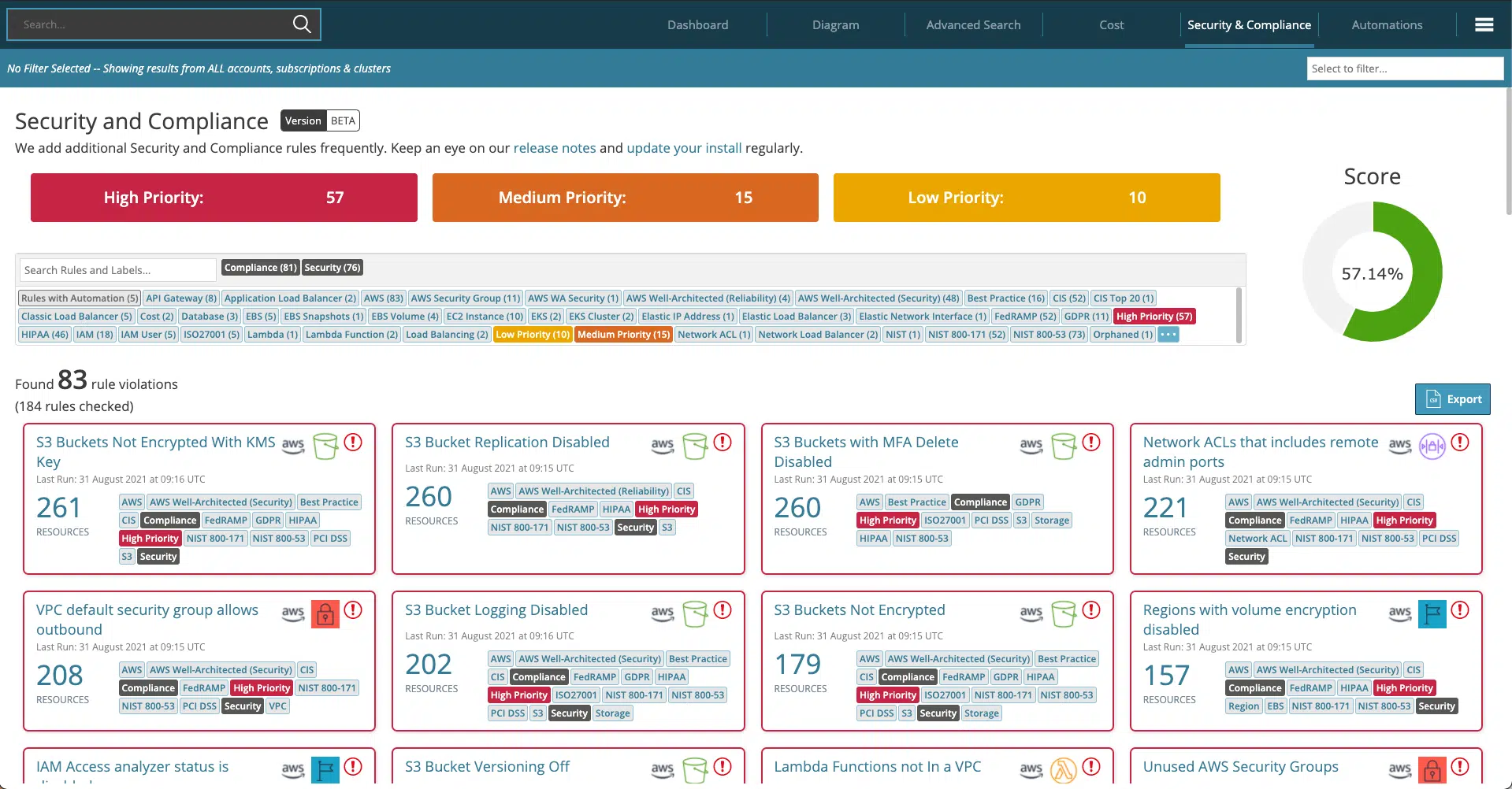
Hyperglance applies hundreds of rules to identify security weaknesses and compliance issues and detect resources misconfiguration based on industry best practices such as NIST 800-53, NIST 800-171, Fedramp, CIS and several other Cloud architectural frameworks.
This is extremely useful for customers requiring frequent audits to ensure compliance with internal policies and best practices.
While Hyperglance ships with control mappings for common compliance standards and regulations, including CIS Foundation Benchmark, PCI DSS, GDPR, HIPAA, FedRAMP, and cloud operational best practices, you can also copy and modify or create your own rules for additional assessment frameworks to help meet your unique regulatory requirements.
You can then export Security and Compliance reports that summarize the obtained evidence collected based on your own rules.
3. Detect
The ability to gather, synthesize, and alert on security-relevant events is fundamental to any cybersecurity risk management program.
This Hyperglance core feature enables timely discovery of security events by continuously monitoring your cloud infrastructure. Hyperglance helps you develop and implement appropriate activities to identify the occurrence of a cybersecurity event.
Examples of outcome Categories within this function include Anomalies and Events, Security Continuous Monitoring, and Detection Processes.
The API-driven nature of Hyperglance provides a new level of visibility and automation. This allows Hyperglance to provide near real-time alerts of compromise or potential compromise while leveraging its unique dependency relationship capabilities to minimize false positives.
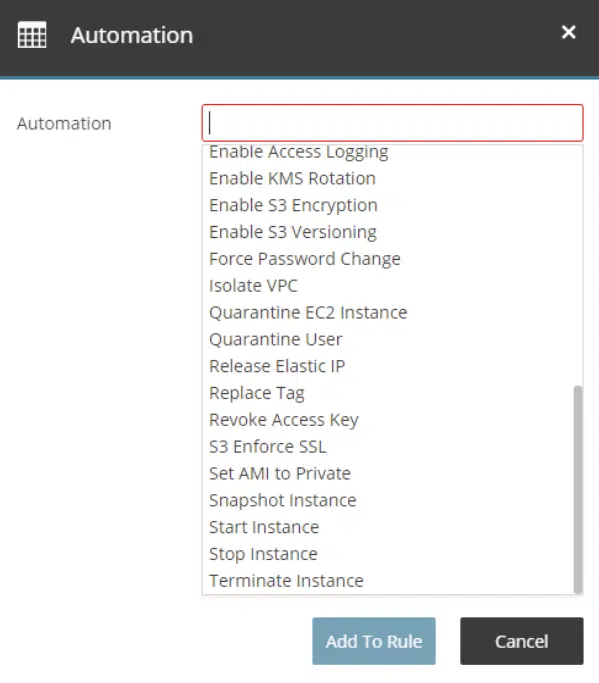
4. Respond
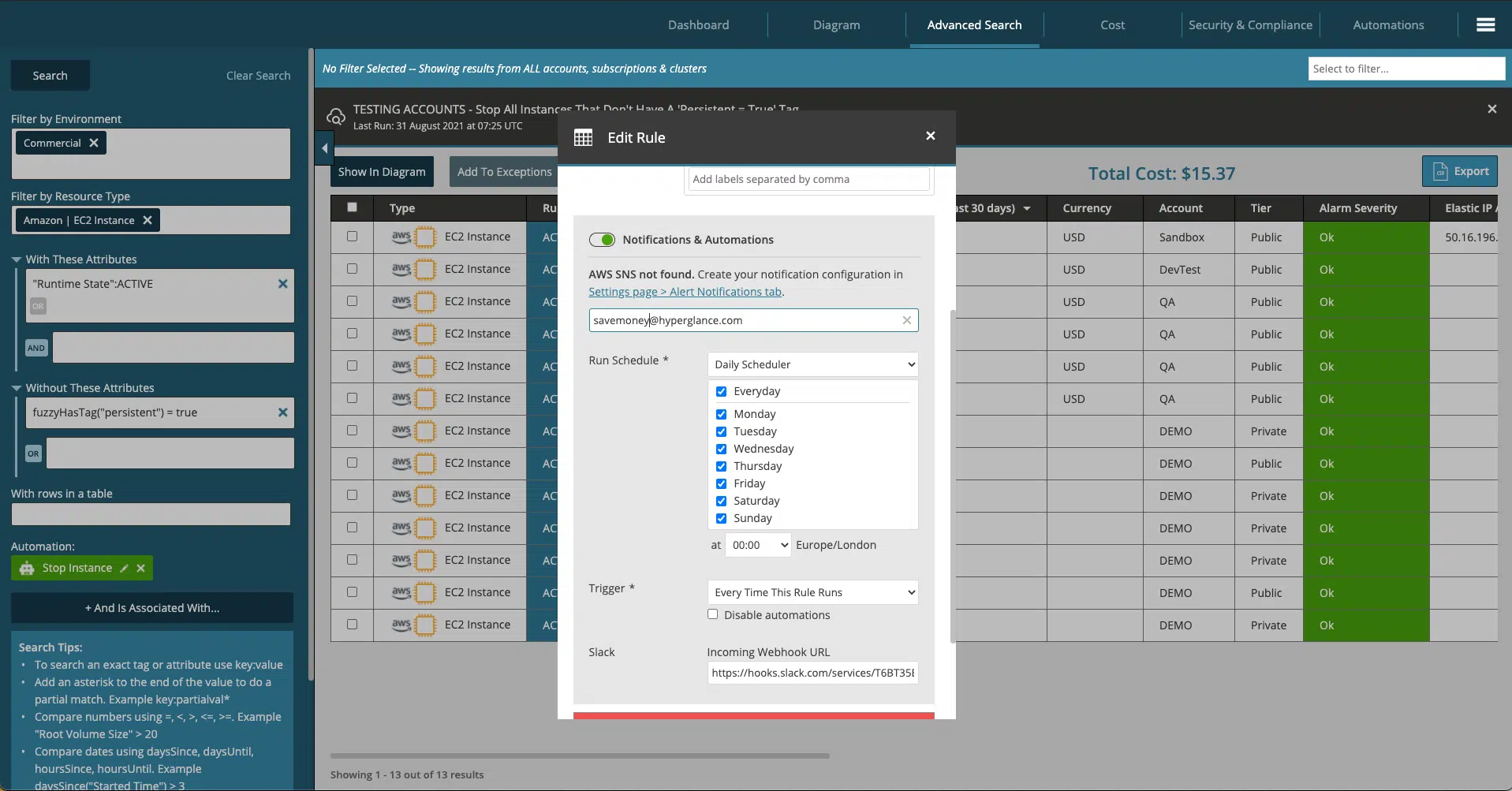
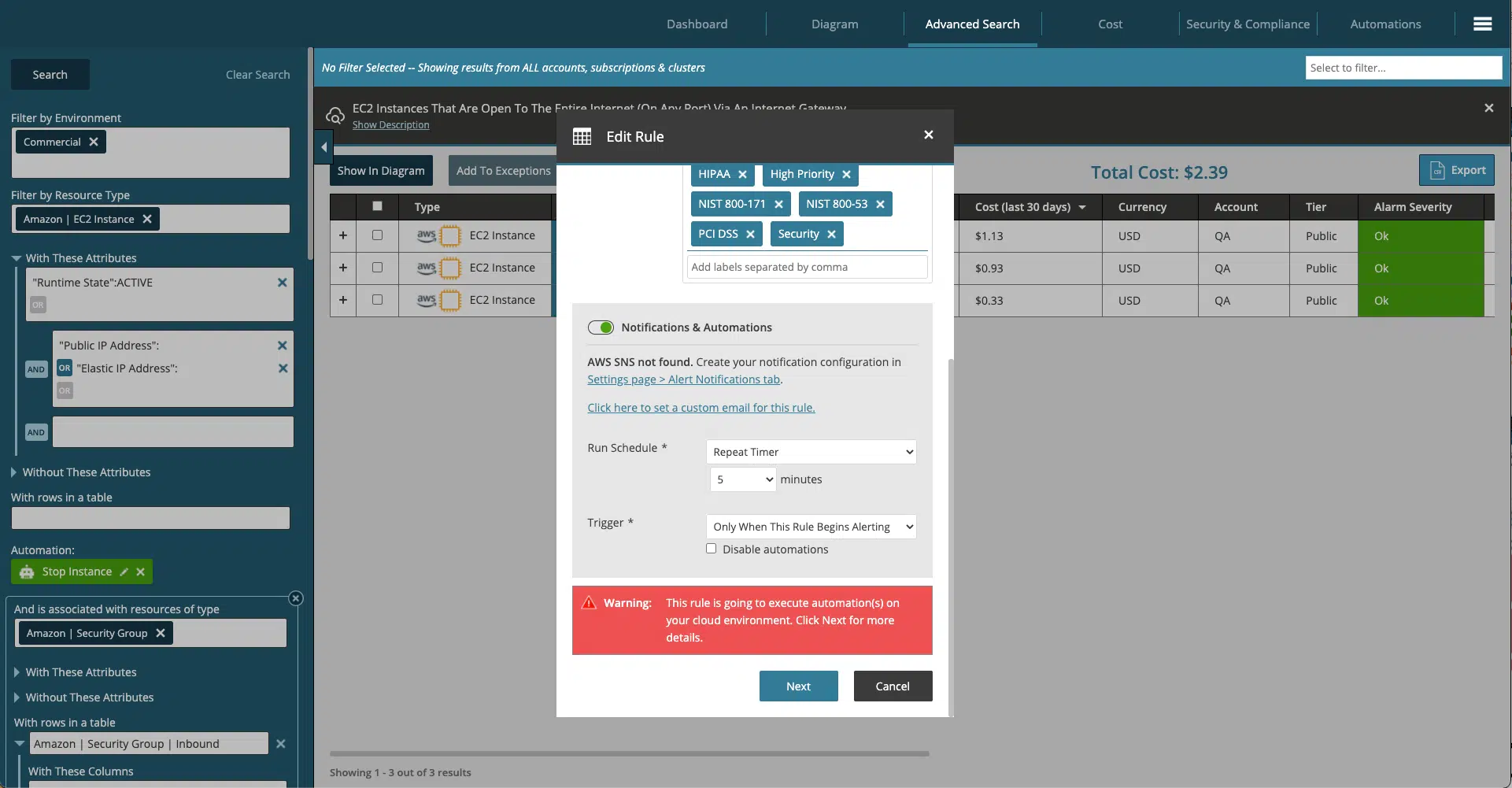
You can use Hyperglance to develop and implement appropriate activities following detected security and compliance incidents.
Its advanced remediation capability helps address the NIST Respond Function by containing the impact of a potential cybersecurity incident.
As the time between detection and response is critical, a well-executed, repeatable response plan minimizes exposure and speeds recovery.
The Hyperglance Automation feature enables the implementation of sophisticated playbooks via the advanced search functionality to minimize the time between detection and response.
5. Recover
Hyperglance ships with hundreds of pre-defined checks. Working in conjunction with the provided automations, which are designed to improve your cloud security posture, these checks help you develop and implement appropriate activities to maintain resilience plans and restore your cloud capabilities that were impaired due to a security or configuration incident.
The combination of a constantly running ruleset, with a flexible automation platform, enables timely recovery to normal operations to reduce the impact of a cloud-related incident.
Hyperglance Automation helps orchestrate the remediation of compliance failures & governance of desired-state security policies.
Conclusion
Cloud management shouldn’t involve guesswork, let alone skilled team members spending time on relatively menial tasks and troubleshooting operational problems. Hyperglance ships with solutions designed to help meet security & compliance policies requirements, optimize cost, and more... all in real-time.
More on Implementing the NIST Cybersecurity Framework
Public and private sector entities acknowledge the security value of adopting the NIST CSF and the need for cost-effective solutions to achieve a secure and compliant system and organizational risk posture in a multi-cloud enterprise environment.
Furthermore, each NIST CSF Function is comprised of one or more Categories, process-specific outcomes that support cybersecurity management. These Categories, in turn, are comprised of numerous specific Subcategories that provide process assessment to determine the current state and target goals
Hyperglance - Cloud Management You Control
Hyperglance gives you complete cloud management enabling you to have confidence in your security posture and cost management whilst providing you with enlightening, real-time architecture diagrams.
Monitor security & compliance, manage costs & reduce your bill, interactive diagrams & inventory, built-in automation. Save time & money and get complete peace of mind.
Book a 30-minute demo today, or experience it all, for free, with a 14-day trial.

About The Author: Stephen Lucas
As Hyperglance's Chief Product Officer, Stephen is responsible for the Hyperglance product roadmap. Stephen has over 20 years of experience in product management, project management, and cloud strategy across various industries.