Improve Your Cloud Security Posture Management (CSPM)
Cloud security posture management provides several important benefits for businesses, including increased visibility into the cloud environment, improved security practices, and better risk management.
When done well, it enables businesses to identify vulnerabilities and threats, respond to incidents more effectively, and comply with relevant regulations and standards.
Effective cloud security posture management also helps businesses to optimize their cloud infrastructure and reduce the risk of data breaches and cyber-attacks, which can result in financial losses and damage to their reputation.
Best-in-class CSPM is essential for businesses that want to ensure the security and integrity of their cloud environment and protect their sensitive data and assets.
CSPM is now a critical aspect of securing your cloud environment. As organizations increasingly embrace the cloud for their infrastructure and applications, it's essential to understand the inherent risks and take proactive measures to protect against potential threats.
We delve into the importance of risk management and threat protection in the context of CSPM and how it can help you secure your cloud environment.
What is Cloud Security Posture Management?
Cloud Security Posture Management (CSPM for short) is a term most likely coined, by research firm Gartner, in a 2019 innovation paper. The term is cloud agnostic - it applies to any cloud platform, including the big three: GCP, AWS and Azure.
In the research paper, Gartner noted that “nearly all successful attacks on cloud services are the result of customer misconfiguration, mismanagement and mistakes.”
So, what is CSPM?
Cloud Security Posture Management (CSPM) is a set of tools/systems and processes/policies that are designed to reduce the risk of a public cloud data or compliance breach.
In the same paper, Gartner specifically referred to CSPM as a new market sector for vendors. The tools that followed were initially designed to explore and monitor PaaS & IaaS environments. The best tools now automatically fix problems, saving SecOps and InfoSec teams valuable time as well as risk.
Gartner & CSPM
Gartner is a leading research and advisory firm known for its in-depth analysis and insights into the IT industry, earning respect for its comprehensive methodologies and influential market evaluations.
Although Gartner was among the first to identify CSPM as a software category, they are yet to add it to their Magic Quadrant or Critical Capabilities lists. Given the growth of CSPM and its market, this is something that seems inevitable to change in the near future.
Magic Quadrant: The Gartner Magic Quadrant is a visual tool that categorizes technology providers in growing markets into four groups: Leaders, Visionaries, Niche Players, and Challengers. Leaders excel in their vision and execution, Visionaries have a forward-looking vision but may lack execution, Niche Players specialize in specific segments, and Challengers perform well currently but may not foresee market trends. This tool helps businesses evaluate and choose suitable market competitors based on their unique needs.
Critical Capabilities: Gartner's Critical Capabilities is a research methodology designed to complement the Magic Quadrant, offering a deeper examination of providers' product and service offerings. This methodology scores competing products or services against a set of essential differentiators identified by Gartner. It helps users understand which products or services best align with specific use cases, providing actionable advice for vendor selection.
While the Magic Quadrant positions vendors in a market, Critical Capabilities delves deeper into the specifics of product and service offerings. Together, these research tools offer a comprehensive view, enabling informed technology decisions.
What Prevents Effective CSPM?
No matter whether you're using AWS, Azure, or GCP, there are a few common factors that stand in the way of effective cloud security posture management.
- Lack of visibility into the cloud environment: Cloud environments can be complex, with multiple services, applications, and users accessing resources from various locations. Without a centralized view of the cloud environment, it can be difficult to identify security vulnerabilities or threat
- Lack of resources and expertise: Many businesses lack the resources to monitor their cloud security posture effectively. They may not have the staff, tools, or knowledge needed to implement security best practices, detect threats, or respond to incidents effectively.
- The ever-changing face of cloud computing: With cloud services evolving rapidly, it can be challenging to keep up with the latest security threats and vulnerabilities. Security protocols and practices that were effective yesterday may be outdated today, leaving businesses exposed to new risks.
- Compliance requirements: Different industries have different regulations and standards that they must comply with, and failure to comply with these requirements can result in severe consequences, including financial penalties and damage to the business's reputation.
How does CSPM Work?
Cloud Security Posture Management (CSPM) provides organizations with a proactive and automated approach to managing security risks throughout their cloud infrastructure.
CSPM uses automated tools and practices to continuously scan, monitor, and assess cloud resources and configurations for potential security threats.
By leveraging industry standards, best practices, and predefined security policies, CSPM finds misconfigurations, vulnerabilities, and policy violations that could pose risks to the security of cloud workloads.
CSPM also offers automated remediation and response capabilities, allowing organizations to quickly address problems they surface, reducing their overall risk exposure.
Best-in-class CSPM tools facilitate organizations to enhance their security posture, minimize security risks, and work towards a completely secure and compliant cloud environment.
Who is Responsible for CSPM?
In a 2020 CISO MAG survey, 76% of respondents believed that their Cloud Service Provider (CSP) was entirely responsible for cloud security.
AWS and Azure, however, have other ideas.
AWS CSPM
AWS’ shared responsibility model makes it clear that the responsibility is split between them and the consumer of their service. They (AWS) are responsible for the security of the cloud, but we (AWS' consumers) are responsible for the security in the cloud.
"AWS is responsible for protecting the infrastructure that runs all of the services offered in the AWS Cloud. This infrastructure is composed of the hardware, software, networking, and facilities that run AWS Cloud services."
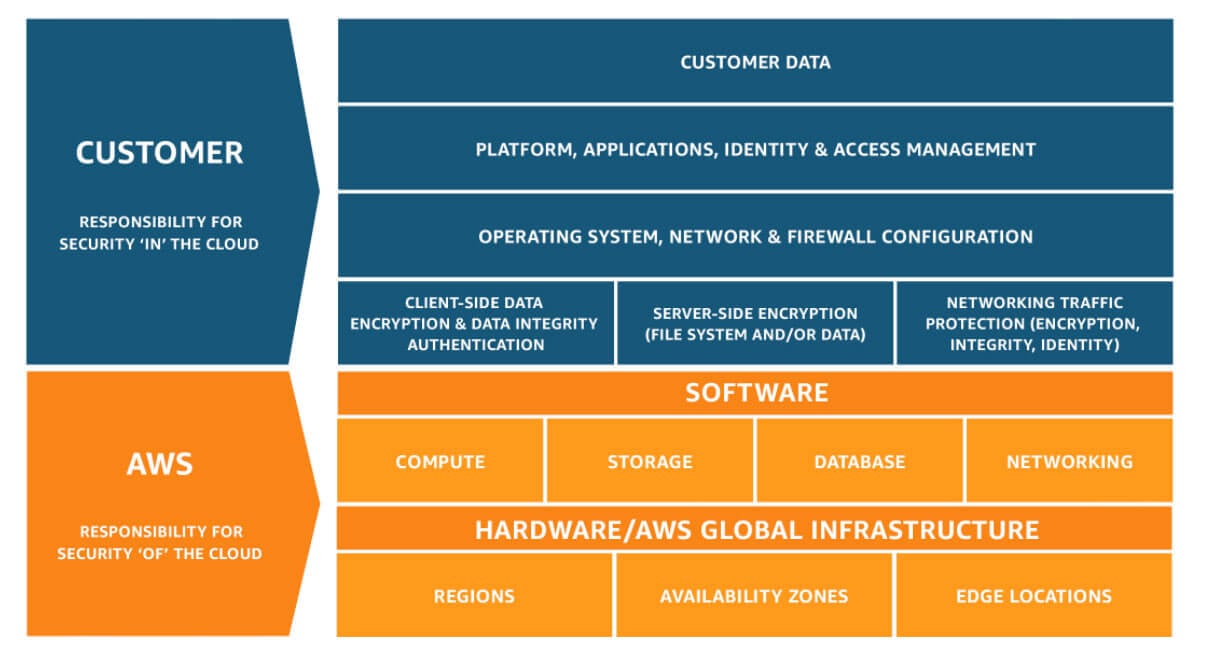
Source: AWS' Shared Responsibility Model
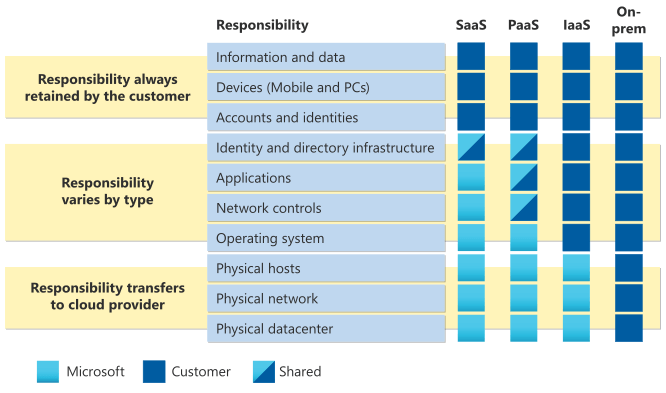
Azure CSPM
When it comes to Azure, Microsoft holds the same view as Amazon.
"In an on-premises data center, you own the whole stack. As you move to the cloud some responsibilities transfer to Microsoft."
The Azure shared responsibility model states that the customer is always responsible for “data, endpoints, accounts, & access management”. The further away you move from on-prem (IaaS, PaaS, then SaaS), the more responsibilities transfer to Microsoft.
Benefits of Cloud Security Posture Management
As cloud and micro-service usage grows, so do the number of unmanaged risks and, sadly, headline-making data breaches. Combine bad headlines with more regulatory standards and policies, and you have a recipe for cloud security that is more complex and higher risk than ever before.
Gartner’s view is that by 2025 “90% of the organizations that fail to control their public cloud use will inappropriately share sensitive data”. That's why CSPM benefits not only your security, but visibility and cost:
Security
Breaches seem to grow in profile year on year. Regulators are becoming less generous in the amount they fine companies that break the rules (whether they intended to break the rules or not).
Class actions are also more frequent, larger, and becoming commonplace in new parts of the globe.
Identify Risks
Understanding the risks associated with your cloud environment is a fundamental step in securing it effectively.
CSPM provides you with the tools and insights to gain visibility into your cloud infrastructure's security and identify potential vulnerabilities or misconfigurations that could expose your organization to risk.
Leverage CSPM and you can assess the security posture of your cloud resources, including VMs, storage accounts, databases, and more, and identify areas that need improvement to reduce the risk of potential threats.
Proactively Manage Risk
One of the key benefits of CSPM is its proactive approach to risk management.
CSPM solutions continuously scan your cloud environment for misconfigurations, vulnerabilities, and compliance violations, allowing you to identify and remediate issues before they can be exploited by threat actors.
With real-time monitoring and automated alerts, CSPM enables you to proactively manage risks and take corrective actions to ensure that your cloud resources are securely configured and compliant with best practices and regulatory requirements.
Threat Protection
Cloud environments are from immune to threats, and organizations must be vigilant in protecting their cloud resources from various cyber threats, including malware, ransomware, data breaches, and insider threats.
CSPM helps organizations protect against these threats by providing continuous monitoring and analysis of cloud resources, identifying anomalous activities, and providing automated threat detection and response capabilities.
Implement CSPM for threat protection, and you can quickly detect and respond to potential security incidents in your cloud environment, minimizing the risk of data breaches or other security breaches.
Holistic Cloud Security Management
CSPM is a critical component of a holistic cloud security management strategy. It enables organizations to effectively manage and monitor the security posture of their cloud environment, identify and mitigate risks, and protect against various threats. By integrating CSPM with other cloud security tools, such as cloud access security brokers (CASBs), security information and event management (SIEM) systems, and identity and access management (IAM) solutions, organizations can create a comprehensive security ecosystem that provides end-to-end visibility and control over their cloud environment.
Securing your cloud environment is ultimately a complex task that requires proactive risk management and threat protection.
CSPM is a powerful tool that can help organizations effectively manage the security posture of their cloud resources, identify and remediate risks, and protect against various threats. By leveraging CSPM as part of a holistic cloud security management strategy, organizations can ensure that their cloud environment is secure and compliant with best practices, minimizing the risk of potential security breaches and protecting their critical assets and data.
Visibility
Visibility into cloud infrastructures is critical for effective threat detection and response. With the increasing complexity and dynamic nature of cloud environments, organizations need robust tools and practices to gain comprehensive visibility into their cloud resources and infrastructure. In this section, we will explore how Cloud Security Posture Management (CSPM) solutions can enhance threat visibility through automation in cloud infrastructures.
Automated Threat Detection and Monitoring
CSPM solutions offer automated threat detection and monitoring capabilities for cloud infrastructures.
Through continuous scanning and monitoring, CSPM solutions can identify misconfigurations, vulnerabilities, and other security risks in real-time. This enables organizations to detect potential threats and security gaps early, allowing for timely remediation to prevent security incidents or breaches.
CSPM also provides visibility into user activities, including authentication attempts, resource changes, and other security-related events, allowing organizations to track and monitor user actions and detect any suspicious activities or unauthorized access.
Comprehensive Infrastructure Visibility
CSPM solutions provide comprehensive visibility into cloud infrastructures, allowing organizations to gain insights into the configuration, resource utilization, and security posture of their cloud workloads. CSPM solutions offer automated assessments and recommendations based on industry standards and best practices, allowing organizations to identify and address security risks across their entire cloud environment. This holistic visibility into cloud resources, infrastructure, and configurations enables organizations to proactively identify and mitigate potential threats, ensuring a secure and compliant cloud environment.
Resource Monitoring & Inventory
CSPM solutions also offer resource monitoring and inventory capabilities, allowing organizations to track and manage cloud resources efficiently.
CSPM can automatically discover and inventory cloud resources, such as virtual machines, storage accounts, databases, and networking components, providing organizations with a comprehensive view of their cloud assets.
This helps organizations track and manage their cloud resources, identify any unauthorized or misconfigured resources, and ensure that all resources are compliant with security policies and best practices.
Automated Remediation and Response
CSPM solutions can automate the remediation and response process for identified threats or security risks. Through automated recommendations and remediation guidance, CSPM enables organizations to quickly and efficiently address security issues, such as misconfigurations, vulnerabilities, or policy violations. This automation helps organizations reduce the time and effort required for manual remediation, minimizing the window of exposure to potential threats and ensuring a timely response to security incidents.
Visibility into cloud infrastructures is essential for effective threat detection and response. CSPM solutions offer automated threat detection and monitoring, comprehensive infrastructure visibility, resource monitoring and inventory, and automated remediation and response capabilities. By leveraging CSPM to enhance threat visibility in their cloud environments, organizations can proactively detect and address security risks, ensuring a secure and compliant cloud infrastructure.
Financial Risk
The cost of fines and legal cases can still be dwarfed by the overnight reputational damage a breach can cause. The cost of data breaches continues to climb at an alarming rate.
Now more than ever is the time to take control of your cloud security.
Compliance isn't a fire drill, it's a 24/7 requirement.
Leverage CSPM as a Powerful Tool For Database Security
Cloud Security Posture Management (CSPM) is an essential solution for securing your cloud environment, including your cloud workloads and databases. With the growing adoption of cloud computing, organizations must prioritize the security of their cloud workloads to protect sensitive data and ensure compliance with industry regulations.
Here's how CSPM can be leveraged as a powerful tool for managing the security of cloud workloads and databases.
Comprehensive Database Security
Databases are critical components of many cloud workloads, storing sensitive data such as customer information, financial records, and intellectual property. Therefore, ensuring the security of your cloud databases is paramount. CSPM provides comprehensive database security capabilities, allowing you to monitor and manage the security posture of your cloud databases effectively.
CSPM solutions can detect misconfigurations, vulnerabilities, and other security risks in your cloud databases, such as open ports, weak passwords, and unencrypted data, and provide automated remediation recommendations to address these issues promptly.
Real-time Monitoring & Alerts
CSPM enables real-time monitoring of your cloud workloads and databases, providing continuous visibility into their security posture. This allows you to quickly detect and respond to potential security incidents, such as unauthorized access attempts, unusual database activities, or data breaches.
CSPM solutions can generate automated alerts and notifications when security risks are identified, allowing you to take proactive actions to mitigate potential threats and protect your cloud workloads and databases from unauthorized access or data breaches.
Automated Compliance Monitoring
Compliance with industry regulations and internal policies is critical for organizations operating in the cloud. CSPM solutions can help you automate compliance monitoring for your cloud workloads and databases, ensuring that they adhere to relevant regulatory requirements, such as GDPR, HIPAA, or PCI DSS.
CSPM solutions provide predefined compliance checks and automated scans to assess the compliance of your cloud workloads and databases against industry standards, and generate reports to demonstrate compliance to auditors and stakeholders.
Service-Specific Security Best Practices
Different cloud service providers (CSPs) offer various cloud services, and each has its unique security considerations and best practices.
CSPM solutions provide service-specific security insights and recommendations to help you adhere to best practices for securing different cloud workloads and databases. For example, CSPM can provide guidance on securing Amazon RDS databases, Azure SQL databases, or Google Cloud Spanner databases, based on their respective security features and configurations. By leveraging CSPM, you can ensure that your cloud workloads and databases are securely configured, reducing the risk of potential security breaches or data leaks.
Data Security
Managing the security of cloud workloads and databases is crucial for organizations operating in the cloud. CSPM serves as a powerful tool for comprehensive workload and database security, offering real-time monitoring, automated alerts, compliance monitoring, and service-specific security best practices. By leveraging CSPM as part of your cloud security strategy, you can effectively manage the security posture of your cloud workloads and databases, mitigate potential security risks, and protect your sensitive data from unauthorized access or data breaches.
How To Choose a CSPM Vendor/Tool
Since Gartner initially coined the term, CSPM tools have come a very long way.
High-profile data breaches regularly reinforce the need for effective CSPM, growing the market size to $9 billion by 2026.
Initially, CSPM tools helped you discover and visualize your IaaS and PaaS asset inventory.
The best CSPM tools now help you save time and minimize risk across your entire stack.
Key Capabilities of a CSPM Vendor/Tool:
With the help of tools like Hyperglance, you can overcome these challenges, and start your journey towards highly effective cloud security posture management that'll be the envy of your industry.
When you're looking for a CSPM tool, make sure it has these features:
- Out-of-the-box compliance with security frameworks such as PCI DSS, HIPAA, SOC 2, GDPR, etc.
- Built-in monitoring using a library of best practices
- Multi-cloud asset discovery, classification, and risk assessment
- Real-time, continuous visualization of your infrastructure
- Protection against common misconfiguration (e.g. expired keys, disabled logging, incorrect permissions, lack of encryption, updates not being run)
- Codeless customizable automation to remediate common issues in real-time
- Continuous delivery whilst enforcing DevOps and DevSecOps policies
Enforcing Compliance with CSPM: Best Practices for Automated Risk Management
Compliance management is a critical aspect of cloud security, as organizations must adhere to industry regulations and internal policies when operating in the cloud. Cloud Security Posture Management (CSPM) can play a vital role in ensuring compliance with these requirements, providing automated risk management capabilities that help organizations maintain a secure and compliant cloud environment.
In this section, we will explore best practices for leveraging CSPM for compliance management in the cloud.
Automated Compliance Monitoring
CSPM solutions offer automated compliance monitoring capabilities that can help organizations streamline their compliance efforts. By leveraging automation, CSPM solutions can regularly scan and assess the security posture of cloud workloads and services against predefined compliance checks, such as GDPR, HIPAA, or PCI DSS.
Automated compliance monitoring allows organizations to identify and address potential compliance gaps promptly, reducing the risk of non-compliance and associated penalties.
Service-Specific Compliance Best Practices
Different cloud service providers (CSPs) have their unique compliance requirements and best practices.
CSPM solutions provide service-specific compliance insights and recommendations to help organizations adhere to these requirements. For example, CSPM can offer guidance on securing Amazon S3 buckets, Azure Virtual Machines, or Google Cloud IAM policies, based on their respective security features and configurations.
Following service-specific compliance best practices can help organizations align their cloud workloads and services with industry regulations and internal policies, ensuring compliance in a multi-cloud environment.
Continuous Monitoring and Remediation
CSPM enables continuous monitoring of cloud workloads and services, allowing organizations to promptly detect and remediate compliance issues.
CSPM solutions provide real-time alerts and notifications when compliance risks are identified, allowing organizations to take immediate actions to mitigate these risks.
CSPM solutions can also offer automated remediation recommendations and actions to address compliance gaps, simplifying the process of maintaining compliance in the cloud.
Policy and Configuration Management
Effective policy and configuration management is essential for compliance in the cloud.
CSPM solutions provide policy and configuration management capabilities that help organizations define and enforce security policies across cloud workloads and services. They can also assess the compliance of cloud workloads and services against predefined policies and configurations, and provide recommendations for remediation.
This enables organizations to maintain a consistent and compliant security posture across their cloud environment.
Audit and Reporting
CSPM solutions provide audit and reporting capabilities that help organizations demonstrate compliance to auditors, regulators, and stakeholders. CSPM solutions generate comprehensive reports that provide visibility into the compliance status of cloud workloads and services, including details on identified compliance issues, remediation actions taken, and overall compliance posture. These reports can be used to demonstrate compliance efforts, track compliance progress, and provide evidence of compliance during audits or assessments.
Compliance management is a critical aspect of cloud security, and CSPM can be a valuable tool for ensuring compliance in the cloud. By leveraging automated compliance monitoring, service-specific compliance best practices, continuous monitoring and remediation, policy and configuration management, and audit and reporting capabilities offered by CSPM solutions, organizations can effectively manage compliance risks in their cloud environment.
By maintaining a secure and compliant cloud posture, organizations can reduce the risk of non-compliance, protect sensitive data, and maintain the trust of their customers and stakeholders.
Choosing a Cloud Security Posture Management Vendor
If you're looking to improve your cloud security posture, Hyperglance is the perfect place to start.
Hyperglance ships with a wealth of features that contribute to successful CSPM:
Customizable Options
Hyperglance includes hundreds of out-of-the-box fully customizable checks, all designed to help you enforce policy and reduce your cloud bill.
Continuous Updates
The checks run continuously, can trigger notifications, and are based on best practices and industry frameworks (CIS, NIST, NIST 800-53, NIST 800-171, AWS Well-Architected, HIPAA, PCI DSS, & FedRAMP).
Automations
Hyperglance also ships with an ever-growing library of cloud automations designed to help you keep your cloud in check, and remediate in real-time.
Flexibility
Hyperglance is self-hosted, deployed through the AWS & Azure Marketplaces (including GovCloud and Azure Government), in Kubernetes, or installed on your own instance/VM.
About The Author: Stephen Lucas
As Hyperglance's Chief Product Officer (CPO), Stephen is responsible for the Hyperglance product roadmap. Stephen has over 20 years of experience in product management, project management, and cloud strategy across various industries.