What is Cloud Compliance?
Cloud compliance might sound daunting, but don't worry, we'll break it down for you. In essence, it's a lot like making sure your car passes its yearly inspection to stay roadworthy. Instead of tires and engines though, we're talking about data and networks.
Cloud Compliance refers to the guidelines and laws designed to protect and regulate information stored on the cloud.
This encompasses several areas, including how data is stored, protected, and used. Whether it's personal data like names and social security numbers, or confidential business information, it's crucial to handle these details responsibly.
Every industry has its own set of rules. For healthcare, it's HIPAA; for payment card data, it's PCI DSS; for anyone handling personal data of EU citizens, it's GDPR. Each set of regulations has its own compliance requirements to ensure that data stored in the cloud is managed correctly and securely.
But it's not just about the legalities, following these standards can help your business improve its cloud security, protect your customers' trust, and even prevent costly fines. In other words, cloud compliance is about driving responsibly and passing your inspections in the world of cloud computing!
Who is responsible for Cloud Compliance & Security?
Azure and AWS are both clear that the responsibility for cloud security is shared.
AWS’ shared responsibility model is clear that the responsibility is split between them and the consumer of their service. They (AWS) are responsible for the security of the cloud, but we (AWS' consumers) are responsible for the security in the cloud.
The Azure shared responsibility model states that the customer is always responsible for “data, endpoints, accounts, & access management”. The further away you move from on-prem (IaaS, PaaS, then SaaS), the more responsibilities transfer to Microsoft.
Key Components of a Cloud Compliance Framework
Cloud compliance frameworks are structured guidelines for securing cloud environments. The key components typically include:
- Policies and Procedures: This outlines the organization's data handling, processing, and storage procedures in the cloud.
- Risk Assessment: Regular checks are done to spot potential risks and vulnerabilities, helping to maintain compliance.
- Security Controls: These safeguards, such as encryption and access controls, ensure the protection of data.
- Regulatory Compliance: This includes meeting specific laws and regulations that apply to your organization's data and operations.
- Incident Response Plan: This sets out steps to take in case of a security incident or data breach.
- Training and Awareness: Regular employee training ensures everyone understands their role in maintaining compliance.
- Auditing and Monitoring: Regular audits and continuous monitoring verify compliance and detect anomalies.
- Review and Improvement: The framework should be frequently reviewed and updated to ensure continued effectiveness and relevance.
Cloud Compliance Frameworks
Here's our list of the most important standards/frameworks in cloud computing:
AWS Well Architected

Ever wished for a roadmap to building a more robust, secure, and efficient cloud architecture? Say hello to the AWS Well-Architected Framework.
In the simplest terms, think of this framework as your trusted guide for constructing high-performing cloud infrastructure. It's a set of strategic guidelines developed by the wizards over at AWS, designed to help cloud architects build the most secure, high-performing, resilient, and efficient infrastructure possible for their applications.
The AWS Well-Architected Framework is organized around six pillars:
- Operational Excellence: This is all about the ability to run and monitor systems effectively, deliver business value, and continually improve supporting processes and procedures.
- Security: As you might expect, this pillar emphasizes protecting information and systems, managing who can do what with privilege management, and implementing controls to detect security events.
- Reliability: This one centers on preventing and recovering from failures to meet demand and achieve business goals.
- Performance Efficiency: The focus here is on using resources efficiently to meet system requirements and maintaining that efficiency as demand changes and technology evolves.
- Cost Optimization: This pillar revolves around avoiding unnecessary costs, and running systems at the lowest price point without sacrificing quality or performance.
- Sustainability: This relatively new pillar is centered on minimizing the environmental impact of running cloud workloads.
By following the advice encapsulated within these pillars, you're not just ticking boxes; you're building a cloud infrastructure that is secure, high-performing, resilient, and efficient. It's like having a cloud guru whispering best practices in your ear. Not bad, right?
FedRAMP (Federal Risk and Authorization Management Program)

Ah, the world of acronyms. FedRAMP stands tall among them, especially if you're navigating the space of cloud services in relation to the U.S. government.
At its core, FedRAMP is a government-wide program standardizing the approach to security assessment, authorization, and continuous monitoring for cloud products and services. That's a mouthful, but in simpler terms, it's a seal of approval, ensuring cloud services have the right level of security to be used by federal agencies.
For cloud professionals, FedRAMP can sometimes feel like a high bar to clear. But once you understand its essence, it's really about maintaining the highest standard of data protection. It follows a "do once, use many times" framework which reduces the efforts, time, and costs that would otherwise be required for the security assessment of a cloud service.
Three levels of security impact are defined in FedRAMP - Low, Moderate, and High, each corresponding to the potential impact of a security breach.
FedRAMP may feel like a tough nut to crack, but it’s worth it. Adhering to its guidelines not only helps you serve government clients but also elevates your overall cloud security posture. So, despite the challenges it may pose, it's a badge of honor in the cloud industry.
HIPAA (Health Insurance Portability and Accountability Act)

Healthcare and cloud computing - a match made in heaven? Well, if you're in the healthcare sector or deal with health-related data in the U.S., you've likely come across the term HIPAA.
HIPAA, or the Health Insurance Portability and Accountability Act, is not a framework like some of our previous entries. Instead, it's a U.S. law designed to provide privacy standards to protect patients' medical records and other health information provided to health plans, doctors, hospitals, and other healthcare providers.
In the context of cloud services, HIPAA applies to cloud providers that process, store, or transmit "Protected Health Information" (PHI). To be considered HIPAA-compliant, cloud providers must implement a robust set of physical, network, and process security measures. Moreover, they need to sign a Business Associate Agreement (BAA) in which they commit to comply with certain provisions of HIPAA rules.
HIPAA compliance might feel like navigating through a maze at times, but it's ultimately about ensuring the privacy and security of sensitive health information. Adhering to its guidelines means you're treating your customers' health data with the care and respect they deserve.
PCI DSS (Payment Card Industry Data Security Standard)

In the realm of digital transactions, one framework tends to stands outl: PCI DSS. If your organization deals with card payments in any form, you're likely already familiar with this one.
The Payment Card Industry Data Security Standard is a set of security standards designed to ensure all companies that process, store, or transmit credit card information maintain a secure environment. It's a universal standard, applicable to entities of all sizes and geographies, as long as they handle cardholder data.
PCI DSS outlines a framework of specifications, tools, measurements, and support resources to help organizations ensure the safe handling of cardholder information. It covers six major objectives which are further broken down into 12 requirements. These range from building and maintaining a secure network, to regularly monitoring and testing networks, to maintaining an information security policy.
In the context of cloud services, both the cloud provider and the customer have a shared responsibility when it comes to ensuring compliance. Cloud providers must secure the underlying infrastructure, while customers must ensure the way they use the cloud services complies with the standard.
While achieving and maintaining PCI DSS compliance might seem like a challenging task, it's a vital part of ensuring the security and trustworthiness of card payment systems.
Interested in product updates, cloud news & tips?
Join the 5,700+ cloud professionals who have signed up for our free newsletter.
By subscribing, you're agreeing that Hyperglance can email you news, tips, updates & offers. You can unsubscribe at any time.
NIST CSF (Cybersecurity Framework)
Imagine having a roadmap for managing and reducing cybersecurity risk at your disposal. That's precisely what the NIST Cybersecurity Framework (CSF) provides.
The National Institute of Standards and Technology, or NIST, is a U.S. federal agency that develops and promotes measurements standards. One of its widely adopted standards is the NIST Cybersecurity Framework - a set of guidelines aimed at helping organizations manage and reduce cybersecurity risk.
The framework isn't a one-size-fits-all approach but is designed to be tailored to meet the specific needs and risks of each organization. It provides a common language for understanding, managing, and expressing cybersecurity risk, both internally and externally.
The NIST Cybersecurity Framework is structured around five core functions: Identify, Protect, Detect, Respond, and Recover. Each function is divided into categories tied to programmatic needs and specific activities to achieve the outcomes for each subcategory.
While it was developed for the U.S., its principles are universal and have been widely adopted globally. In a cloud context, organizations can use the NIST Cybersecurity Framework to assess and improve their ability to prevent, detect, and respond to cyber-attacks involving their cloud resources.
So whether you're a small business or a multinational corporation, the NIST Cybersecurity Framework offers a valuable guide to navigate the complex landscape of cybersecurity risks.
GDPR (General Data Protection Regulation)
If you've ever dealt with data of EU citizens, then GDPR is likely a term that has kept you up at night.
The General Data Protection Regulation, or GDPR, is a regulation enacted by the European Union to protect the privacy and personal data of its residents. Despite being an EU regulation, it has global implications. Any organization, regardless of its location, that processes the personal data of individuals within the EU must comply.
GDPR is centered on principles such as transparency, lawful basis for processing, data minimization, accuracy, storage limitation, integrity and confidentiality, and accountability. It grants EU citizens specific rights like the right to access their personal data, the right to rectification, the right to be forgotten, and more.
In the cloud context, both the cloud provider and the customer share responsibility for ensuring GDPR compliance. Cloud providers must ensure they provide GDPR-compliant services, while customers must use those services in a GDPR-compliant way.
Complying with GDPR may seem daunting, but it's an essential part of modern data handling practices. It not only ensures the privacy of EU citizens but also cultivates trust between organizations and their users.
CIS Critical Security Controls

Formerly known as the CIS Top 20, there are now 18 CIS Critical Security Controls. In the field of information security, the Center for Internet Security (CIS) controls stand as a respected guide for securing a wide variety of systems and platforms, including cloud environments.
CIS Benchmarks are a set of best practices for the secure configuration of a system. Developed by a community of IT professionals, they offer in-depth guidance backed by extensive research and testing. Covering over 100 systems and platforms, the CIS Benchmarks provide a robust tool for organizations to enhance their security posture.
For each system or software, the CIS Benchmarks provide a series of recommendations and a clear guide on how to implement them. They cover all aspects of a system, from its initial setup and installation, through its ongoing management and maintenance, down to its auditing and logging.
In the context of cloud environments, specific CIS Benchmarks exist for cloud platforms such as AWS, Azure, and Google Cloud. These benchmarks provide detailed guidance for securely configuring these cloud environments and using their services safely.
Although following the CIS Benchmarks may seem like a daunting task, the security benefits they offer make it a worthwhile endeavor. They are an invaluable resource for cloud professionals aiming to maintain high standards of security within their cloud environments.
FISMA (Federal Information Security Modernization Act)

When it comes to U.S. government agencies, there's one act that rings particularly loud: the Federal Information Security Modernization Act, or FISMA.
Established in 2002, FISMA requires federal agencies to develop, document, and implement an information security and protection program. But its scope isn't limited to government bodies. If you're an organization that handles federal data, this is an act you'll need to comply with, as well.
FISMA lays out a clear framework for managing information security that revolves around risk management and the need to secure information systems that support the operations and assets of an agency. This includes systems managed by third parties on behalf of a federal agency.
In the cloud environment, both cloud service providers and their customers share the responsibility of ensuring FISMA compliance. Cloud providers must ensure their services meet FISMA requirements, while customers must ensure they use these services in a manner that complies with the Act.
While FISMA compliance might seem like an uphill task, it's an essential part of protecting sensitive federal data. Plus, it can enhance your organization's overall security posture.
ISO 27001
In a world where data is the new oil, protecting it becomes paramount. This is where ISO 27001 steps in.
ISO 27001 is an international standard that provides a robust framework for establishing, implementing, operating, monitoring, reviewing, maintaining, and improving an Information Security Management System (ISMS). It was developed by the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC).
The standard outlines a risk management process involving the identification and assessment of risks to the confidentiality, integrity, and availability of information. Controls are then applied to reduce these risks to an acceptable level.
ISO 27001 is technology-neutral and uses a top-down, risk-based approach. The standard is particularly significant in the cloud environment as it ensures that the cloud service provider follows a systematic approach to managing sensitive company information and ensuring data security.
Becoming ISO 27001 certified can seem like a daunting task, but the journey can significantly improve your organization's resilience against information security threats and enhance customer and stakeholder confidence in your cloud security posture.
SOX (Sarbanes-Oxley Act)
Stepping into the realm of financial reporting, we encounter the Sarbanes-Oxley Act, or SOX. Born out of major corporate and accounting scandals in the early 2000s, SOX is a U.S. law aimed at protecting investors from fraudulent financial reporting by corporations.
SOX establishes strict auditing and financial regulations to protect shareholders and the general public from accounting errors and fraudulent practices. While it isn’t strictly about information technology or cloud computing, it has significant implications for IT departments and cloud service providers.
Under SOX, corporate IT departments are required to create and maintain systems of internal controls to assure the integrity and confidentiality of data, as well as the accuracy of financial reports. These controls should ensure that all financial transactions are tracked accurately and that no data is altered or deleted.
In a cloud context, both the cloud service provider and the customer share the responsibility for ensuring SOX compliance. While the cloud provider must ensure their infrastructure is secure and reliable, customers must ensure their usage of cloud services complies with the Act’s requirements.
SOX compliance can seem daunting, but it's an essential part of maintaining trust in your organization's financial activities. Plus, the practices it promotes can enhance your overall security and reliability.
Azure Well Architected

Much like a skilled artist refining a masterpiece, ensuring your cloud architecture is well-structured and efficient is an art in itself. Enter the Azure Well-Architected Framework - a set of guiding tenets designed to help you construct and optimize robust and efficient solutions on Azure.
This framework, developed by Microsoft, provides a set of best practices and actionable guidance. It's divided into five pillars that resonate with those from AWS, but with a touch of Azure-specific insights:
- Cost Optimization: This pillar emphasizes managing and controlling costs to maximize the value delivered.
- Operational Excellence: This pillar focuses on operations processes that keep a system running smoothly and adapting to changes.
- Performance Efficiency: This one is about system performance, specifically, ensuring that systems can adapt their performance as needed efficiently.
- Reliability: This pillar looks at the system's ability to recover from failures and continue to function.
- Security: This one, unsurprisingly, is all about protecting applications and data from threats.
The Azure Well-Architected Framework provides a valuable methodology for evaluating your architectures and implementing designs that scale over time. By aligning your solutions to the principles in the framework, you can ensure that they're built on a solid foundation that caters to business needs while maximizing the benefits of the Azure platform.
Google Cloud Architecture Framework
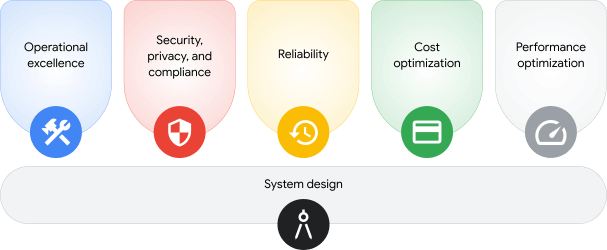
In the increasingly competitive world of cloud platforms, Google Cloud holds its own, complete with its very own guiding star - the Google Cloud Architecture Framework.
This framework, developed by Google, offers a structured approach to creating, architecting, designing, and implementing cloud solutions. It provides a comprehensive and authoritative set of best practices that guide you in making the right choices for your applications running on Google Cloud.
The Google Cloud Architecture Framework is built around five key pillars:
- Security: This pillar emphasizes creating secure and private application architectures that ensure data protection and compliance with industry standards.
- Reliability: This focuses on developing reliable and resilient systems that effectively manage outages and continue to function in their intended, correct manner.
- Performance optimization: This pillar is all about ensuring that your applications meet your performance objectives, both now and in the future.
- Cost Optimization: This focuses on creating cost-effective systems that give you the most value from your Google Cloud investments.
- Operational excellence: This pillar focuses on efficient deployment, monitoring, and operation of cloud workloads.
The Google Cloud Architecture Framework offers a holistic approach to designing, implementing, and managing solutions in Google Cloud. By aligning your solutions to the principles in this framework, you're ensuring they're built on a solid foundation and take full advantage of what Google Cloud has to offer.
Hyperglance - Cloud Management You Control
Hyperglance gives you complete cloud management enabling you to have confidence in your security posture and cost management whilst providing you with enlightening, real-time architecture diagrams.
Monitor security & compliance, manage costs & reduce your bill, interactive diagrams & inventory, built-in automation. Save time & money and get complete peace of mind.
Book a 30-minute demo today, or experience it all, for free, with a 14-day trial.

About The Author: Stephen Lucas
As Hyperglance's Chief Product Officer (CPO), Stephen is responsible for the Hyperglance product roadmap. Stephen has over 20 years of experience in product management, project management, and cloud strategy across various industries.

