Tags are one of the simplest ways to make AWS spend easier to understand and control.
When they’re planned well, they help you allocate costs, answer ownership questions faster, support governance, and automate routine decisions.
When they’re inconsistent, cost reports get messy, chargeback becomes manual, and teams lose trust in the data.
This guide walks through a practical AWS tagging strategy for FinOps teams. We’ll cover how AWS tags work, which tags to start with, how to avoid tag sprawl, where AWS cost allocation tags fit, and how to keep your standards useful as your cloud estate grows.
In this guide, we’ll show you how to build a practical tagging strategy that supports cost allocation, ownership, governance, and automation.
Azure Tags + GCP Labels
Although we wrote this guide for AWS tags, the same approach works across clouds.
Azure uses tags. GCP uses labels. The goal is the same: consistent metadata that helps you answer “Who owns this?”, “What is it for?”, and “Should we still be paying for it?”
| AWS | Azure | GCP |
|---|---|---|
| Tags | Tags | Labels |
| Account | Subscription | Project |
| Cost allocation tags | Cost allocation via tags | Billing by labels (where supported) |
| Tag key/value | Tag name/value | Label key/value (more restricted) |
| Enforce at creation | Policy to enforce | Policy/constraints to enforce |
What are AWS Tags?
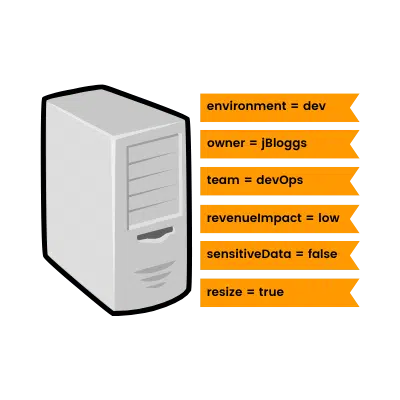
AWS tags are labels that can be applied (optionally) to resources, including EC2 instances, S3 buckets, AMIs, and lots more. They are a simple way to add context to a resource.
Each tag comprises a key and a value, both of which you generate.
Their flexibility means that tags are a hugely valuable form of metadata and a great tool to help organizations manage their cloud architecture.
When done well, tagging is much more than just a just time-saving way to search and filter through your resource inventory. A comprehensive tagging strategy will help you understand your AWS usage, reduce your costs, monitor your performance, and manage your risk.
Tags also facilitate a cross-team focus, so each area of your organization can hone in on their area of responsibility. Whether you need a helicopter view or a detailed FinOps dashboard, resource tags are at the heart of it all.
Examples of keys include a resource's owner, environment, or project... the possibilities are virtually limitless, though.
Here are some examples in the format key = value:
-
owner = engineering
-
project = marketingWebsite
-
environment = production
-
businessUnit = 016
-
sensitiveData = true
-
application = fin-app-1
-
resize = false
Note for Azure & GCP
If you’re in Azure, treat this as the same concept: tags on resources that make ownership and cost reporting possible.
If you’re in GCP, you’ll usually talk about labels. Keep label keys consistent, or your billing views split into lots of near-duplicates.
What Good AWS Tags Help You Answer
Good tags should help you answer a few basic questions quickly:
- Who owns this resource?
- Which application or workload does it support?
- Which environment is it in?
- Which cost center or business unit should pay for it?
- Does it handle sensitive or regulated data?
If your tags don't make those answers easier to get, your schema probably needs work.
What Format is an AWS Tag?
A single AWS resource can have up to 50 tags applied to it. AWS generated tags are the one exception; these are automatically generated, cannot be edited, and don't count towards the limit of 50.
Each tag comprises a key and a value, both of which you define.
System-generated AWS tags that aren't editable have keys beginning 'aws', e.g.
aws:createdBy
The tags we are mainly concerned with, user-generated tags, normally don't have anything populated before the key you have created, e.g.
environment
NB: In the wild, in some AWS reports, you might spot 'user' being prefixed before your key, e.g. user:environment. This is to differentiate your user-created tags from AWS' system-generated ones for the sole benefit of the reports.
A key is mandatory for all tags; they can be up to 128 Unicode (UTF-8) characters long. Tag values are actually optional and can be up to 256 Unicode (UTF-8) characters long.
The characters permitted in both keys & values vary slightly per AWS service, but in general UTF-8 letters, numbers and spaces are accepted, along with these special characters:
_ . : / = + - @.
Tag keys must be unique on a resource, and each key can only have one value.
Importantly, tag keys & values are case sensitive (more on this later).
Why You Need a Tagging Strategy
A tagging strategy is a set of policies and processes, with reference points, that your team or organization agree to implement and live by.
Ultimately, your strategy is there to define how tags should be used in your AWS (and Azure) architecture.
Put simply, a best-in-class tagging strategy...
- Saves money
- Reduces risk
- Improves efficiency & agility
- Facilitates automation
- Provides clarity & answers questions
What are the Benefits?

With the addition of codeless cloud automation tools, like Hyperglance, tagging opens more doors than ever before.
We've included some great examples of how you can benefit from a tagging strategy, but the sky is the limit. Get a good team together for some ideation, and you'll amaze yourself with the problems you can solve (often within minutes!).
Save Money
- Use tags for resource allocation, e.g. owner, team, project, or cost center
- Use tags to help resource owners analyze their costs and plan/forecast for the future
- Find resources that were intended to have a temporary lifespan
- Find resources that aren't used 24/7, and should be automatically started and stopped
- Use resources to manage EC2 reserved instances and identify RI recommendations
- Enable cost-allocation tags, and use them in combination with Cost Explorer and a cloud management tool to identify many other cost-saving opportunities
Reduce Risk
- Tag resources based on their data/security risk, regulatory requirement, or internal policies
- Tag resources to manage IAM access/permissions
- Tag resources with owners to speed up decision making in critical situations
- Use tags in rules & conditions to implement monitoring & alerts, reducing increasingly common 'alert fatigue'
- Find resources that need updating
- Use a clear strategy to lead the way for your future organizational standards
Improve Efficiency
- Categorize resources to solve problems faster. Combine tags with a tool that simplifies your inventory, diagrams your cloud, and has a superior search function to AWS' own.
- Use tags to trigger automation and alerting. Start by identifying your team's most menial tasks and see how you can automate them.
- Tag resources based on how often they need manually reviewing
- Use tags to identify resources that should be opted out of certain automated tasks
- Use a clear strategy as the foundation to free up decision-makers, increasing your team's agility (and creativity!)
- Tag business-critical resources to improve operational focus and clarity, and adhere to SLAs
- If you're subject to audits, no matter internal or external, tag the relevant resources to save swathes of time processing auditor requests (not to mention managing the day-to-day operational risk of those resources)
- Quickly answer common questions from other people/teams in your organization, e.g.
- How much does it cost to support this project?
- Which team owns the most high-risk resources?
- Who should I contact about a problem with this resource?
- How many critical servers need updating?
- Which resources should we stop at the weekend?
AWS Cost Allocation Tags: Start with the Few You Trust
Not every tag needs to become a cost allocation tag.
Start with the tags that finance and engineering both trust, such as owner, application, environment, and costCenter.
Activate those first in AWS Billing, use them in Cost Explorer and reporting, and only expand the list when the data stays clean for a few reporting cycles.
This gives you a better base for showback, chargeback, and budget conversations without forcing a huge schema on day 1.
AWS Tagging Best Practices
The recipe for a great tagging strategy is no secret. Here are the ingredients:

1. Plan Your Tag List
Nail this stage and everything after becomes easier.
Realistically, in most organizations, you'll have stakeholders with requirements from a cross-section of teams.
Think about who has sufficient technical experience and could provide valuable input from areas such as:
- Compliance & security
- Finance
- IT operations & disaster recovery
- Database admin
- Engineering & product
- Process & business unit owners
When you get your team together, start by thinking about the outcomes you'd like, as opposed to the tags you want.
You're less likely to miss requirements if you work backwards from outcomes such as 'I want to be able to find & monitor resources that store sensitive data', versus jumping straight to a solution like 'I want a tag for resources that store sensitive data'. After discussion, the former might lead you to suggest a useful scale; the latter is more likely to end up as a less-detailed binary outcome.
Each desired outcome (requirement) should be mapped to propose a new/existing tag. And for each of those tags, make sure you know the answer to these questions:
- What will the tag be used for?
- Who will use the tag (people & system)?
- When will the tags be used?
- How will the tag be added?
- Who should have permission to add/edit/delete the tag?
- Who are the tag's stakeholders?
- What format will the tag key take?
- What format will the tag value take?
- How can the tag be future-proofed?
If you have one available, a technical business analyst is a good person to have around at this stage. They are trained in eliciting requirements from stakeholders, and tend to be strong at documentation.
You'll quickly come up with the desired list of tag keys and possible values.
Start with a Small Mandatory Set
Start with a small required set.
In most teams, 4 to 6 mandatory tags is enough to get real value without slowing delivery.
A solid starting point is:
- owner
- application
- environment
- costCenter
- dataClassification
Only make a tag mandatory when all 3 of these are true:
- You know who owns the value
- You know how the tag will be used
- The value cannot be derived reliably elsewhere
In case you're low on ideas, here are some handy tag keys that you might be able to apply in your organization:
Technical Tag Keys
These help engineers find and manage resources, e.g.
- Name (could be derived from other system data)
- Owner (potentially derivable from Application/Service metadata)
- Application
- Environment
- Cluster
- Version
- SLA (could be derived from a central SLA definition)
Business Tag Keys
These help stakeholders plan and analyze, e.g.
- Team/Department (could derive from project info)
- Project
- Process
- Customer
- Cost Center (could derive from service data)
- Business Unit (could derive from Owner)
- Revenue Impact
- Business Impact
- Managed By
Security Tag Keys
These ensure compliance, minimize risk, and save time in audits, e.g.
- Data Classification
- Compliance Classification
- Security Impact
Automation Tag Keys
These can be used to automate a resource start/stop and deletion, send alerts, schedule patches, exclude resources from resizing, and more, e.g.
- Start/stop date-time
- Review date-time
- Process opt-in/opt-out
A Simple Starter Tag Schema
Here is a simple example of a starter schema for a production workload:
- owner = platform-team
- application = customer-portal
- environment = production
- costCenter = fin-042
- dataClassification = confidential
- reviewDate = 2026-07-01
This is not a universal template, but it shows the level of clarity you should aim for.
2. Document Definitions & Standards
Plenty of people will live and die by this documentation, so make sure you give it its due.
Here are our essential tips for the documentation itself:
- Use a collaboration-friendly tool, such as Confluence
- Make sure that the standards are peer-reviewed for clarity & accuracy from time to time
- Add a worked example for every required tag
Keep a simple changelog so teams can see what changed and why - Make sure there is a simple process for stakeholders to ask questions and request changes
- Review the tags with stakeholders regularly
For each tag, we'd recommend recording this information:
- The tag key, including spelling and casing
- The tag value, including spelling, casing, and possible options (where there is a fixed list worth communicating)
- The tag's purpose
- Whether each tag is mandatory or optional
- Useful background, e.g. who requested the tag, when was it implemented or last changed
- The tag's owner/decision-makers and related permission/rules
3. Agree & Implement Governance
By now, you should have an owner recorded for each of your tags. That person should understand the tag's value, and be empowered to make decisions about changes to it. It's ok if they don't make the changes, but they should be signing them off.
The next step, once you've agreed on your governance, is to implement it using IAM (Identity and Access Management). Start with a review of your tag permissions, then use rules & conditions to fine-tune how your tags work within AWS.
When you're allocating permissions in IAM, remember to think about who can change the tag editing permissions, not just the editing of the tag itself.
If you use AWS Organizations, tag policies are a good way to standardize key names, casing, and allowed values across accounts. Start with the tags that matter most for cost allocation and ownership, rather than trying to enforce everything at once.
This helps you cut down near-duplicate tags and bad casing without creating too much friction too early.
4. Tag Broadly, but Keep Required Tags Lean
Try to tag most resources, but be stricter about which tags are mandatory. In practice, a small required set usually gives you better data than a long wish list.
By all means, tag broadly, but only make a tag required when it supports a clear reporting, governance, or automation need.
If a value can be derived reliably from another source, do not force people to type it in by hand.
If there are exceptions, document them clearly.
5. Don't Store Sensitive Data in Tags
This might sound obvious, but it's easily forgotten.
Tag names are prone to be shared via one of the many AWS services you use, often accidentally, maybe deliberately. If you choose to store sensitive or confidential data in your tag names, don't expect the data to stay secure for long.
AWS themselves make it pretty clear:
"Do not add personally identifiable information (PII) or other confidential or sensitive information in tags. Tags are accessible to many AWS services, including billing. Tags are not intended to be used for private or sensitive data."
6. Pick a Naming Convention and Stick to It
Consistency matters more than whether you choose lowerCamelCase or lowercase-with-hyphens. We prefer lowerCamelCase for tag keys because it is readable and common in AWS-heavy environments.
The important part is picking one standard, documenting it clearly, and enforcing it.
AWS tag keys and values are case sensitive, so inconsistent casing will break reporting, filtering, and automation faster than most teams expect.
Case... closed?
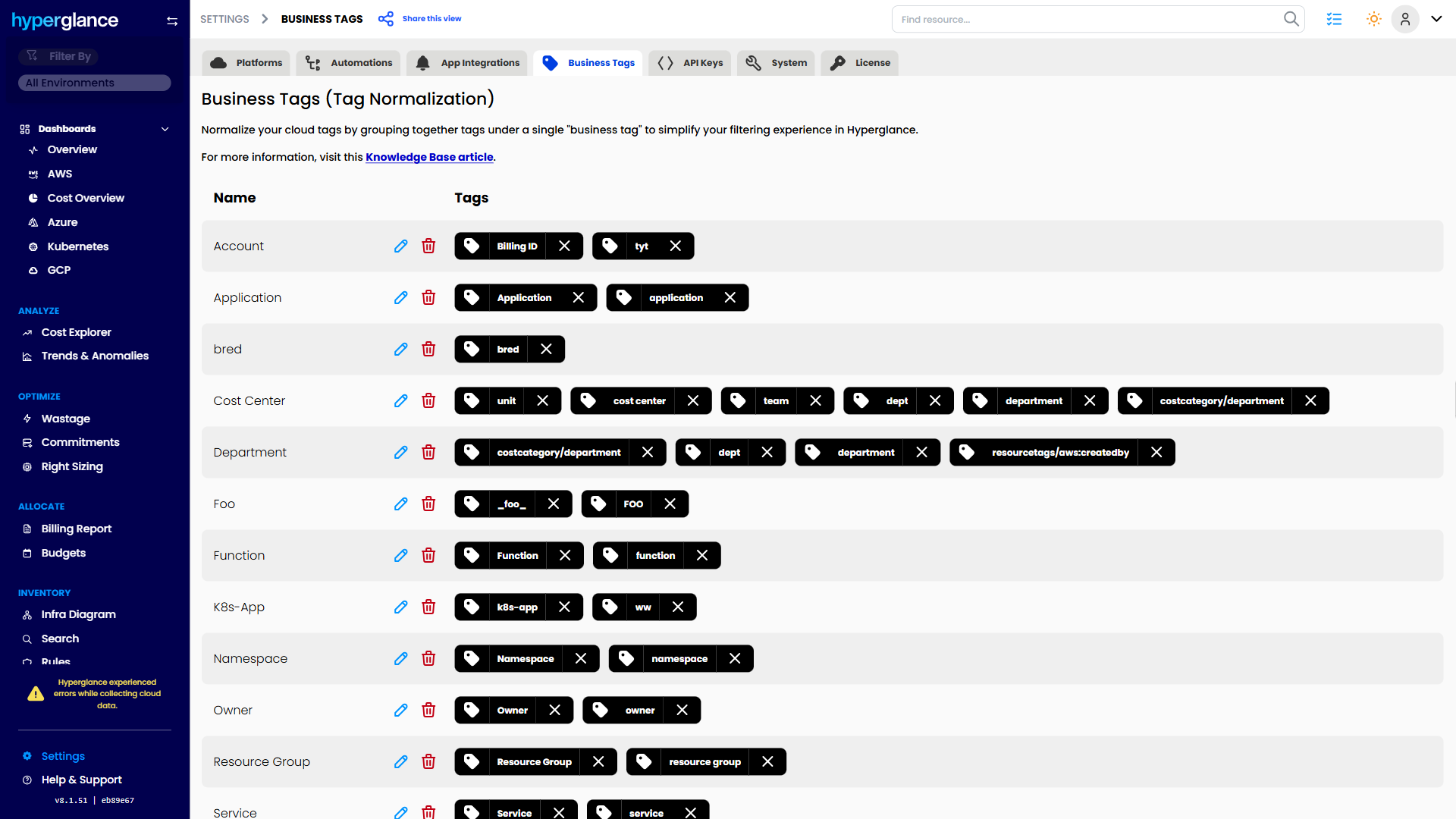
7. Use a Tool to Normalize Tags
Best-in-class cloud management tools give you the ability to group tags.
This allows you to configure related tags, making it easier to manage and analyze resources and... account for (inevitable) errors.
This grouping can help normalize typos and inconsistencies in casing. All of this is possible in the app itself - no need to change the tags on your actual resources!
A screenshot of Hyperglance's Tag Normalization Settings
8. Change Tags in Bulk
The AWS Management Console comes with its own tag editor, which allows you to apply changes to tagging in bulk, saving valuable time. It's great for rectifying mistakes that have snowballed, or applying new tags to lots of resources.
If you're wasting time finding and fixing tagging problems, you should go a step further and use a tool that automates your tag updates.
9. Use a Future Proof Schema
When you're planning your tags, be sure to include business information that you can refer back to in the future. Technology and projects change constantly, but concepts such as 'purpose' and 'cost center' remain constant.
For each key, consider whether to have binary values, e.g. true/false or a fixed list of permissible values, e.g. high/medium/low.
Also, be sure you are clear about your use (or non-use) of enum values. As your organization grows, so might its tendency to prefer using enum values that are less likely to be broken by localized language and culture.
Lastly, even if you aren't multi-cloud yet, try and keep tag keys agnostic of your cloud service provider. Someone will thank you for it one day.
10. Think Beyond AWS
Azure and GCP work much like AWS here, so it’s worth planning for multi-cloud from day one.
Azure tags: You’ll see the same problems as AWS, missing owner tags, inconsistent values, and tags added once and then forgotten.
GCP labels: Same goal, but labels tend to be more strict. That’s a good thing. It pushes you towards controlled keys and values.
If you want one tag set across all clouds, avoid cloud-specific keys like awsAccountId or ec2Role. Use neutral keys like Owner, Application, and Environment.
If you already have messy tags across AWS, Azure, and GCP, Hyperglance Virtual Tags can group and normalize them without changing the underlying resources.
11. Monitor & Automate
Naturally, you're going to encounter a few challenges after implementing your strategy.
Firstly, the adoption will take time. Maintaining it thereafter is perhaps an even more complex beast, but it doesn't have to be.
- Plant the seed of consistency by including tagging requirements in CloudFormation templates
- Use AWS config, or a specialist tool, to monitor your resources, and alert you when something isn't right, e.g. missing or badly formatted tags (configure alerts wisely to avoid alert fatigue)
- When something goes wrong, use automation to put it right. With the progression in cloud management tools, there is very little value in a human constantly looking for bad and missing tags, let alone fixing them.
Set a monthly tag hygiene review. Check for missing required tags, invalid values, duplicate keys caused by casing, and tags that are no longer useful.
For existing environments, give teams a short cleanup window before you auto-remediate, unless the issue is already breaking cost reporting or policy.
Common Challenges
As you might have already found out, implementing a tagging strategy can be challenging.
Here are some of the most common obstacles you'll encounter.
1. Starting With The Right People
As with any project, the difference between success and failure can be the stakeholder list. Spend time thinking about the potential decision-makers, as well as those who might be indirectly affected by your proposal (negatively or positively!).
Consider using lightweight project management or business analysis frameworks and tools to help you agree on your foundation, including decision-makers, benefits, and the requirements themselves.
Even if you're not adept at requirements analysis or project management, tools like BOSCARD terms of reference are relatively easy to digest and translate to your organization.
2. Getting Teams to Adopt the Standard
A tagging strategy often fails because teams do not see tagging as part of delivery. Developers care about shipping. Finance cares about cost visibility. Security cares about control. Your schema needs to connect with those real goals.
Tie required tags to things people already care about, such as cost allocation, environment ownership, start and stop schedules, incident response, or compliance checks. Then make the right values easy to find in templates, docs, and examples.
3. Updating & Reviewing Standards
You'll be doing well if this doesn't become a problem at least once in the first few months.
Implementing your initial standards will be half the challenge - keeping them relevant and updated will be something you'll need to become comfortable with.
As a starting point, when you first agree on your standards, ask the team how regularly they'd like to review them. Every time you meet, check that the cadence is still ok.
4. Overtagging or 'Tag Creep'
If your list of mandatory tags is starting to look excessively large, it's probably time to reassess things. Maybe those tags are taking the place of valuable cost-saving or security tags? Even if they aren't, there's a good chance that your teams will be struggling to uphold the standards.
Do what you can to figure out what's causing the tag 'creep'. A common reason is too many teams sharing an account, something that can also complicate management as you scale up your resources over time. Perhaps temporary tags aren't being deleted once a project is complete? Or, dare we say, maybe someone got trigger happy in Pascal case?
5. Finding the Right Balance Between Enforced and Derived
While enforced tags provide a solid foundation for governance and reporting, relying on too many can lead to operational bottlenecks and suboptimal data quality.
A balanced approach—where only the most critical tags are mandatory and additional metadata is derived from existing sources—can offer agility and accuracy in managing your cloud resources.
6. Not Utilizing Helpful Tools
As you start to scale your tagging strategy throughout your organization, implementing the standards becomes more complex and time-consuming. You'll quickly want to monitor for missing tags, typos, and more.
If you're going to take on a large manual edit, do the sensible thing and use the Tag Editor in your AWS console. If you're automating deployments, include your tagging requirements in CloudFormation templates.
Best-in-class tag strategies now comprise tools (e.g. Hyperglance and, to a lesser extent, AWS Config) that monitor tag standards, alert you to problems, and automatically fix them.
FAQs
What Are Tags in AWS?
Tags in AWS are key-value pairs attached to resources. They help you organize infrastructure, track ownership, and support cost allocation, governance, and automation.
What Are AWS Cost Allocation Tags?
AWS cost allocation tags are tags you activate in AWS Billing so AWS can use them in cost reporting. They help you group spend by things like owner, application, project, or cost center.
What Is an AWS Tag Policy?
An AWS tag policy is an AWS Organizations feature that helps standardize tag keys, values, and casing across accounts. It is useful when you need more consistency at scale.
Conclusion
Good AWS tagging is not about adding more metadata for the sake of it. It is about making your cloud estate easier to understand, govern, and act on.
When your tags are clear, consistent, and tied to real business needs, cost allocation gets easier, ownership becomes clearer, and automation becomes far more useful. Teams spend less time arguing over messy reports and more time making informed decisions.
The hard part is not coming up with tag ideas. It is creating a standard people will actually use, then keeping it useful as your environment changes.
Start small. Focus on the tags that support cost allocation, ownership, governance, and reporting first. Then build from there.
And once your tagging strategy is in place, make sure you can see where it is working, where it is breaking down, and where it needs cleanup. That is where the real value starts to show.
Need a clearer way to monitor tagging quality and use tags in cost reporting, search, and automation? Hyperglance can help.
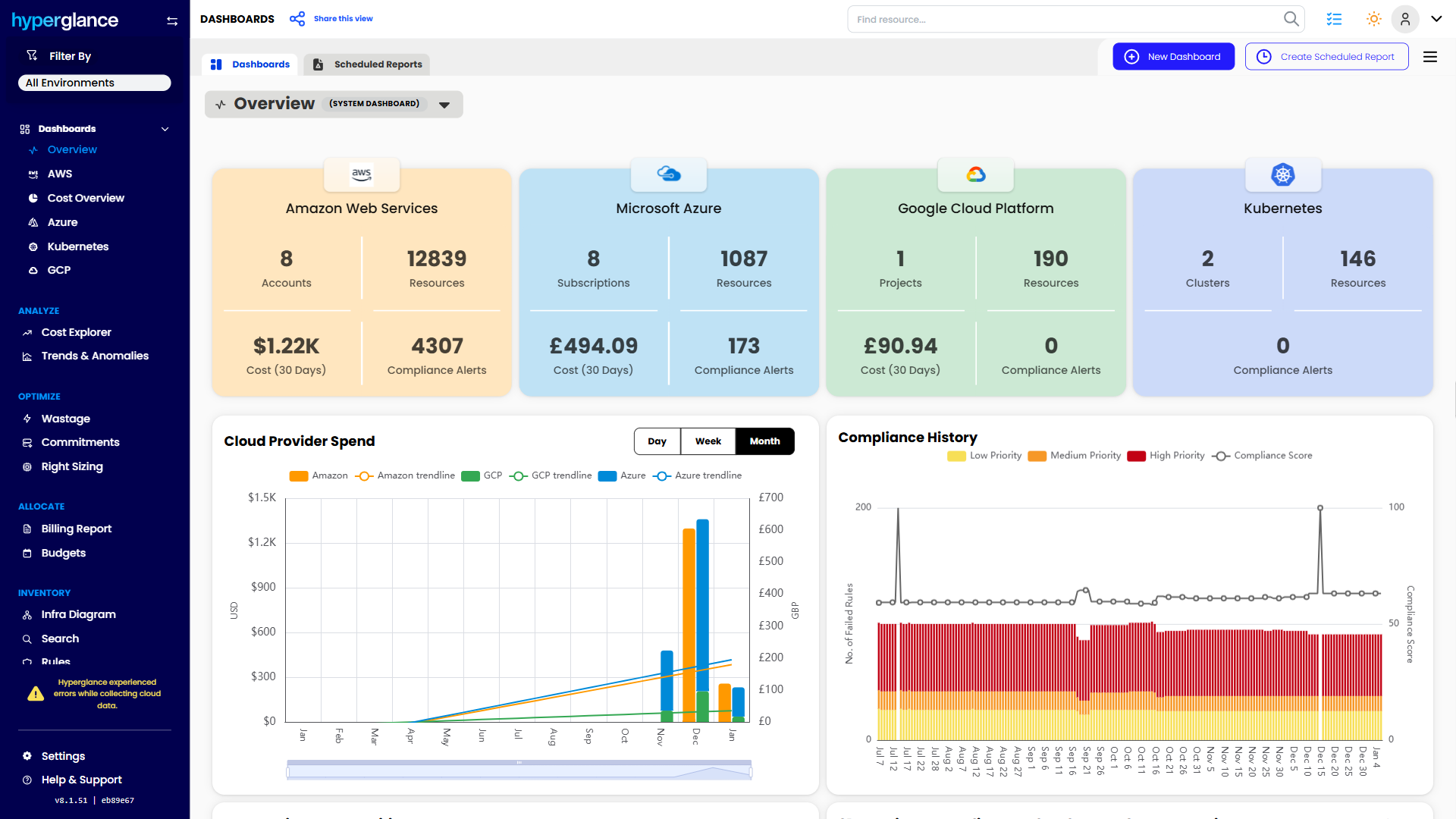
Why Teams Choose Hyperglance in 2026
Hyperglance is a strong fit when cost data alone doesn’t give your team enough context.
That often happens when teams are asking questions like:
- What is running across our cloud estate?
- Who owns this resource?
- Why did this cost change?
- What else depends on it?
- Is this safe to clean up?
- Which policy, security, or compliance issue needs attention?
- Can we route this to the right owner or trigger an approved action?
We help teams connect cloud cost to infrastructure context across AWS, Azure, Google Cloud, and Kubernetes. That means FinOps, CloudOps, platform, security, and leadership teams can work from the same view.
Hyperglance is especially useful for mid-market, enterprise, MSP, public sector, and regulated environments where ownership, governance, automation, and data control matter.
What You Can Do With Hyperglance
- See cost, resources, relationships, and ownership in one place
- Visualize cloud architecture with interactive diagrams
- Find waste, policy issues, and cost anomalies faster
- Route findings to the right team through existing workflows
- Use no-code automation for approved fixes
- Run Hyperglance in your own environment when data control matters
Want to see where Hyperglance fits in your FinOps stack?
Explore the product, start a free trial, or book a demo with the team.

About The Author: David Gill
As Hyperglance's Chief Technology Officer (CTO), David looks after product development & maintenance, providing strategic direction for all things tech. Having been at the core of the Hyperglance team for over 10 years, cloud optimization is at the heart of everything David does.